Entra ID authentication
Microsoft Entra IDauthentication supports the following authentication methods:
-
Entra ID cloud-only identities
-
Entra ID hybrid identities that support:
-
Cloud authentication with two options coupled with seamless single sign-on (SSO)
- Entra ID pass-through authentication
- Entra ID password hash authentication
-
Federated authentication
-
Further details can also be found here.
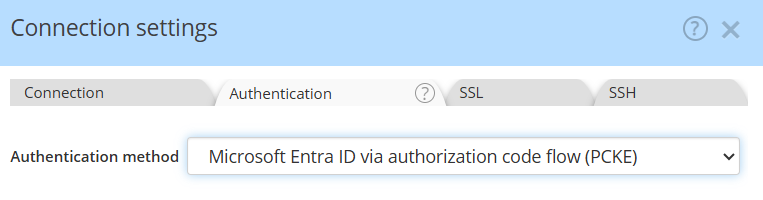
In the Authentication tab of the connection settings dialog, select the applicable Entra ID code flow authentication method:
Granting admin consent
With the Entra ID methods, whether with Username/Password or with MFA, the Azure administrator must grant tenant-wide admin consent to the Hackolade Studio application, as per the documentation page. Here is a shortcut to the admin consent URL for Hackolade Studio.

Your IT admin must give consent in order to allow you access to the database. Consent is required once for the organization.
Legacy username/password
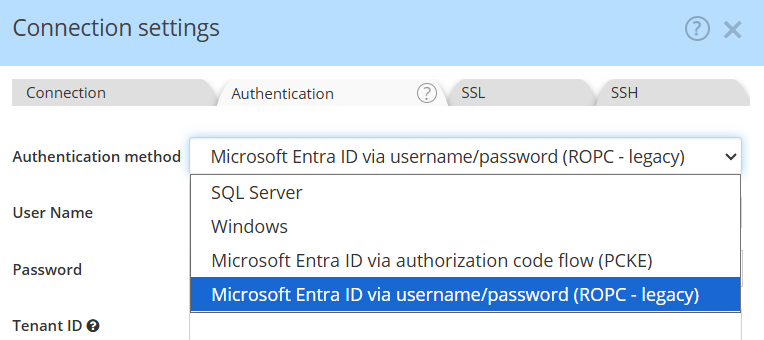
In the Authentication tab of the connection settings dialog, select the applicable Entra ID legacy authentication method, then provide the username/password and Tenant ID:
See instructions on how-to find your tenant ID.